LDAP security
To use Lightweight Directory Access Protocol (LDAP) for user security, you must switch from the default Pentaho security to LDAP, then you must configure LDAP.
Switch to LDAP
Procedure
From the User Console Home menu, click Administration, then select Authentication from the left.
The Authentication interface appears. Local - Use basic Pentaho Authentication is selected by default.Select the External - Use LDAP / Active Directory server option.
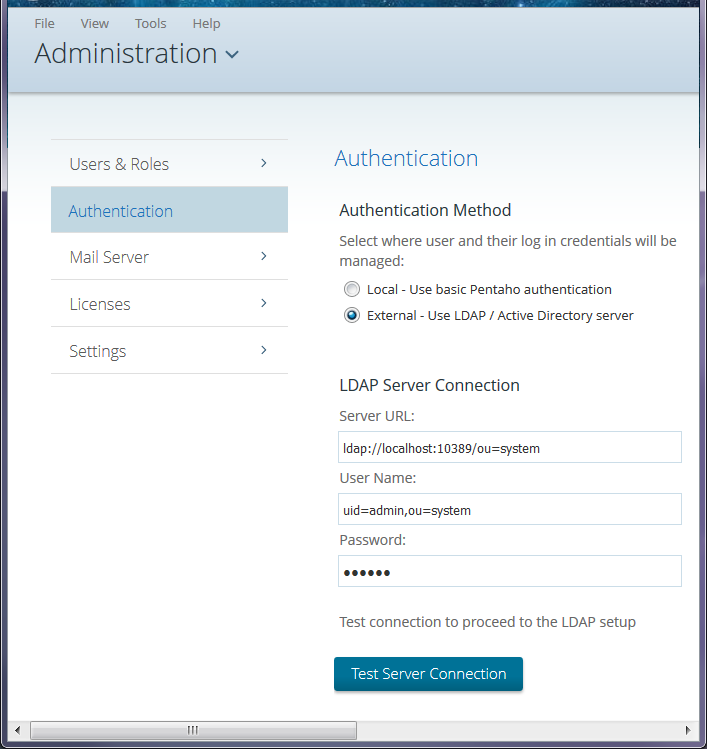 The LDAP Server Connection fields
populate with a default URL, user name, and password.
The LDAP Server Connection fields
populate with a default URL, user name, and password.Change the Server URL, User Name, and Password as needed.
Click Test Server Connection to verify the connection to your LDAP server and to complete the set up.
Click the node to select the Pentaho System Administrator user and role to match your LDAP configuration, then click OK.
NoteThe Admin user is required for all system-related operations, including the creation of user folders. The Administrator Role is required for mapping a third-party admin role to the Pentaho admin role (Administrator). This is required for all ABS functionality to work properly.Select your LDAP Provider from the drop-down menu.
Configure the LDAP connection as explained in LDAP properties.
Delete the server/pentaho-server/pentaho-solutions/system/karaf/caches folder.
Restart the Pentaho Server and test the LDAP functionality.
Results
Manual configuration
Procedure
Stop the Pentaho Server.
Edit the securities.properties file located in the server/pentaho-server/pentaho-solutions/system folder.
Change provider=jackrabbit to provider=ldap
Save and close the file.
Edit the server/pentaho-server/pentaho-solutions/system/applicationContext-security-ldap.properties file.
Modify the settings to match your LDAP configuration.
userSearch.searchBase=OU\=YourDomainCustomerCareUsers,DC\=YourDomainCustomerCare,DC\=com allAuthoritiesSearch.roleAttribute=cn allAuthoritiesSearch.searchBase=OU\=YourDomainCustomerCareGroups,DC\=YourDomainCustomerCare,DC\=com userSearch.searchFilter=(sAMAccountName\={0}) allUsernamesSearch.searchFilter=objectClass\=Person allAuthoritiesSearch.searchFilter= (objectClass\=group) providerType=ldapCustomConfiguration contextSource.userDn=youradminUser@YourDomaincustomercare.com populator.rolePrefix= allUsernamesSearch.searchBase=OU\=YourDomainCustomerCareUsers,DC\=YourDomainCustomerCare,DC\=com adminUser=CN\=YourAdminUserDN,OU\=OrlandoFL,OU\=NAMER,OU\=Support,OU\=YourDomainCustomerCareUsers,DC\=YourDomainCustomerCare,DC\=com adminRole=CN\=YourAdminRole,OU\=YourDomainCustomerCareGroups,DC\=YourDomainCustomerCare,DC\=com populator.groupSearchBase=OU\=YourDomainCustomerCareGroups,DC\=YourDomainCustomerCare,DC\=com populator.convertToUpperCase=false populator.searchSubtree=false allUsernamesSearch.usernameAttribute=sAMAccountName populator.groupRoleAttribute=cn contextSource.providerUrl=ldap\://10.100.7.17\:389 contextSource.password=******** populator.groupSearchFilter=(member\={0})Save and close the file.
Edit the server/pentaho-server/pentaho-solutions/system/repository.spring.properties file.
Replace admin in the following line:
singleTenanatAdminUserName=adminwith the value of the adminUser’ssAMAccountName as defined in the applicationContext-security-ldap.properties file.Save and close the file.
Delete the following directory: server/pentaho-server/pentaho-solutions/system/jackrabbit/repository
CautionDo not delete the repository.xml file, which is also located in the following directory: server/pentaho-server/pentaho-solutions/system/jackrabbitDelete the server/pentaho-server/pentaho-solutions/system/karaf/caches folder.
Restart the Pentaho Server and test the LDAP functionality.
Results
Use nested roles
Procedure
Stop the Pentaho Server or service.
sh /usr/local/pentaho/server/pentaho-server/stop-pentaho.sh
Open the /pentaho/server/pentaho-server/pentaho-solutions/system/applicationContext-spring-security-ldap.xml file with a text editor.
In the
populatorbean definition, replace DefaultLdapAuthoritiesPopulator with: NestedLdapAuthoritiesPopulator<bean id="populator" class="org.pentaho.platform.plugin.services.security.userrole.ldap.NestedLdapAuthoritiesPopulator">
Save the file, then edit /pentaho/server/pentaho-server/pentaho-solutions/system/applicationContext-pentaho-security-ldap.xml.
This and the next step are only necessary if the roles that serve as "parents" to nested roles cannot be returned by a traditional all authorities search.Add an
extraRolesbean to the list of transformers in theChainedTransformersbean, and set properties for each parent role (represented by example_role below).<bean id="allAuthoritiesSearch" class="org.pentaho.platform.plugin.services.security.userrole.ldap.search.GenericLdapSearch"> <!-- omitted --> <constructor-arg index="2"> <bean class="org.apache.commons.collections.functors.ChainedTransformer"> <constructor-arg index="0"> <list> <bean class="org.pentaho.platform.plugin.services.security.userrole.ldap.transform.SearchResultToAttrValueList"> <!-- omitted --> </bean> <bean class="org.pentaho.platform.plugin.services.security.userrole.ldap.transform.ExtraRoles"> <property name="extraRoles"> <set> <value>example_role</value> </set> </property> </bean> <bean class="org.pentaho.platform.plugin.services.security.userrole.ldap.transform.StringToGrantedAuthority"> <!-- omitted --> </bean> </list> </constructor-arg> </bean> </constructor-arg> </bean>Save the file, close your text editor, and start the Pentaho Server.
sh /usr/local/pentaho/server/pentaho-server/start-pentaho.sh
Results
LDAP properties
You can configure LDAP values by editing the /pentaho-solutions/system/applicationContext-security-ldap.properties file in your Pentaho Server folder.
Connection information (context)
| LDAP Property | Purpose | Example |
| context.Source.providerUrl | LDAP connection URL | contextSource.providerUrl=ldap://holly:389/DC=Valyant,DC=local |
| contextSource.userDn | Distinguished name of a user with read access to directory | contextSource.userDn=CN= Administrator,
CN=Users,DC=Valyant,DC=local |
| contextSource.password | Password for the specified user | contextSource.password=secret |
Users
{0} token will be
replaced by the user name from the login dialog box.| LDAP Property | Purpose | Example |
| userSearch.searchBase | Base (by user name) for user searches | userSearch.searchBase=CN=Users |
| userSearch.searchFilter | Filter (by user name) for user searches. The attribute you specify here must contain the value that you want your users to log into Pentaho with. Active Directory user names are represented by sAMAccountName; full names are represented by displayName. | userSearch.searchFilter=(sAMAccountName={0}) |
Populator
{0} token will be replaced with the user DN found
during a user search; the {1} token is replaced with the user name entered
in the login screen.| LDAP Property | Purpose | Example |
| populator.convertToUpperCase | Indicates whether or not retrieved role names are converted to uppercase | populator.convertToUpperCase=false |
| populator.groupRoleAttribute | The attribute to get role names from | populator.groupRoleAttribute=cn |
| populator.groupSearchBase | Base (by user DN or user name) for role searches. | populator.groupSearchBase=ou= Pentaho |
| populator.groupSearchFilter | The special nested group filter for Active Directory is shown in the example; this will not work with non-MSAD directory servers. | populator.groupSearchFilter= (memberof:1.2.840.113556.1.4.1941:
=({0})) |
| populator.rolePrefix | A prefix to add to the beginning of the role name found in the group role attribute; the value can be an empty string. | populator.rolePrefix= |
| populator.searchSubtree | Indicates whether or not the search must include the current object and all
children. If set to false, the search must include the current
object only. | populator.searchSubtree=true |
All authorities search
| LDAP Property | Purpose | Example |
| allAuthoritiesSearch.roleAttribute | The attribute used for role values | allAuthoritiesSearch.roleAttribute=cn |
| allAuthoritiesSearch.searchBase | Base for "all roles" searches | allAuthoritiesSearch.searchBase=ou=
Pentaho |
| allAuthoritiesSearch.searchFilter | Filter for "all roles" searches. Active Directory requires that the objectClass value be set to group. | allAuthoritiesSearch.searchFilter=
(objectClass=group) |
All user name search
| LDAP Property | Purpose | Example |
| allUsernamesSearch.username Attribute | The attribute used for user values | allUsernamesSearch.username Attribute=
sAMAccountName |
| allUsernamesSearch.searchBase | Base for "all users" searches | allUsernamesSearch.searchBase= CN=users |
| allUsernamesSearch.searchFilter | Filter for "all users" searches | allUsernamesSearch.searchFilter=
objectClass=person |

