Security Issues
The following tips provide help with adjusting log file output, examining logs for signs of configuration errors, and possible issues and related solutions during LDAP configuration:
- Increase security log levels in the Pentaho Server
- Log output security analysis
- LDAP roles issues with admin and authenticated
- With LDAP authentication, the PDI Repository Explorer is empty
- LDAP incorrectly authenticates user IDs that do not match letter case
- Connection timeout issues when using CAS
See Pentaho Troubleshooting articles for additional topics.
Increase security log levels in the Pentaho Server
The security logging facilities of the Pentaho Server are set to ERROR by default, which may not supply enough details for troubleshooting and testing.
Procedure
Stop the Pentaho Server with the following script
sh /usr/local/pentaho/server/pentaho-server/stop-pentaho.sh
Open the /pentaho/server/pentaho-server/tomcat/webapps/pentaho/WEB-INF/classes/log4j2.xml file with a text editor.
Change or add the ThresholdFilter value in the
<Console>or <RollingFile> sections to one of the following logging levels:WARN,ERROR,FATAL, orDEBUG(depending on which level you prefer):< Console name="PENTAHOCONSOLE" > <ThresholdFilter level="ERROR"/> <PatternLayout><Pattern>%d{ABSOLUTE} %-5p [%c{1}] %m%n</Pattern> </PatternLayout> </Console>Add the following log statements directly above the root element:
<!-- all Spring Security classes will be set to DEBUG --> <Logger name="org.springframework.security" level=”DEBUG”> <!-- all Pentaho security-related classes will be set to DEBUG --> <Logger name="org.pentaho.platform.engine.security" level=”DEBUG”> <Logger name="org.pentaho.platform.plugin.services.security" level=”DEBUG”>
Save and close the file, then edit the Spring Security configuration file that corresponds with your security back end in the /pentaho/server/pentaho-server/pentaho-solutions/system/ directory. The file will be one of the following options:
- applicationContext-spring-security-memory.xml
- applicationContext-spring-security-jdbc.xml
- applicationContext-spring-security-ldap.xml
Find the
daoAuthenticationProviderbean definition, then add the following property anywhere inside of it (before the</bean>tag):<property name="hideUserNotFoundExceptions" value="false" />
Save the file and close the text editor.
Start the Pentaho Server with the following script:
sh /usr/local/pentaho/server/pentaho-server/start-pentaho.sh
Results
Next steps
Enable extra LDAP security logging
Procedure
Go to the /pentaho/server/pentaho-server/pentaho-solutions/system directory and open the applicationContext-spring-security-ldap.xml file with a text editor.
Locate the bean declaration for
DefaultLdapAuthenticationProviderand replace theconstructor-argbean with the following new bean:Old Bean:
<constructor-arg> <ref bean="authenticator" /> </constructor-arg>
New Bean:
<constructor-arg> <ref bean="ldapAuthenticatorProxy" /> </constructor-arg>
In the same directory, locate and open the pentaho-spring-beans.xml file.
Add the following import line to the list of files:
<import resource="applicationContext-logging.xml" />
Save and close the file.
Locate the /pentaho-server/tomcat/webapps/pentaho/WEB-INF/classes directory and open the log4j2.xml file with a text editor.
Add this category to the log4j2.xml file.
<Logger name="org.springframework.security.providers" level="DEBUG"/>
Save and close the file, then start the Pentaho Server.
Results
Log output security analysis
The following examples help to determine the location of security configuration issues in the pentaho.log:
- When you request a page that is protected, but you are not yet logged on,
you should see an exception in the log which looks like the following
text:
DEBUG [ExceptionTranslationFilter] Access is denied (user is anonymous); redirecting to authentication entry point org.springframework.security.AccessDeniedException: Access is denied - When the user name and/or password does not match what is stored in the
back end, you should see a log message like the following
text:
WARN [LoggerListener] Authentication event AuthenticationFailureBadCredentialsEvent: suzy; details: org.springframework.security.ui.WebAuthenticationDetails@fffd148a: RemoteIpAddress: 127.0.0.1; SessionId: 976C95033136070E0200D6DA26CB0277; exception: Bad credentials - When the user name and password match, you should see a log message that
looks like the following
example:
WARN [LoggerListener] Authentication event InteractiveAuthenticationSuccessEvent: suzy; details: org.springframework.security.ui.WebAuthenticationDetails@fffd148a: RemoteIpAddress: 127.0.0.1; SessionId: 976C95033136070E0200D6DA26CB0277 DEBUG [HttpSessionContextIntegrationFilter] SecurityContext stored to HttpSession: 'org.springframework.security.context.SecurityContextImpl@2b86afeb: Authentication: org.springframework.security.providers.UsernamePasswordAuthenticationToken@2b86afeb: Username: org.springframework.security.userdetails.ldap.LdapUserDetailsImpl@d7f51e; Password: [PROTECTED]; Authenticated: true; Details: org.springframework.security.ui.WebAuthenticationDetails@fffd148a: RemoteIpAddress: 127.0.0.1; SessionId: 976C95033136070E0200D6DA26CB0277; Granted Authorities: ROLE_CTO, ROLE_IS, ROLE_AUTHENTICATED'
InteractiveAuthenticationSuccessEvent, one of the filters will
show the roles fetched for the authenticated user. Compare these roles to the page-role
mapping found in the filterInvocationInterceptor bean in
applicationContext-spring-security.xml.If you are troubleshooting LDAP problems, look for log output similar to the following text:
DEBUG [DirMgrBindAuthenticator] (LoggingInterceptor) Return value: LdapUserInfo:
org.springframework.security.providers.ldap.LdapUserInfo@1f31c64[dn=uid=suzy,ou=users,ou=system,attributes={mail=mail:
suzy.pentaho@pentaho.org, uid=uid: suzy, userpassword=userpassword: [B@e17c9c,
businesscategory=businesscategory: cn=cto,ou=roles,ou=system, cn=is,ou=roles,ou=system,
objectclass=objectClass: organizationalPerson, person, groupOfUniqueNames,
inetOrgPerson, top, uniquemember=uniquemember: cn=cto, ou=roles, cn = is , ou = roles,
sn=sn: Pentaho, cn=cn: suzy}]LDAP roles issues with Admin and Authenticated
Open /pentaho-solutions/system/applicationContext-spring-security.xml in a text editor. At the bottom of this file, you will find a number of entries that look like:
A/docs/.*Z=Anonymous,Authenticated
These
are entries for URL security. They are regular expressions to match a path on the browser’s
URL that require the user to be a member of the defined role to gain access. For this
example, both Anonymous and Authenticated gain
access.
We replace Authenticated with pentahoUsers
by entering A/docs/.*Z=Anonymous,pentahoUsers. For all entries that
show Authenticated, replace it with pentahoUsers or
your chosen name. Replace Admin with pentahoAdmins
or your chosen name.
For the change from Authenticated to
pentahoUsers, replace all occurrences. For Admin to
pentahoAdmins you need to be a little more careful because there are some
entries that look like this: A/admin.*Z=pentahoAdmins.
Edit the /pentaho-solutions/system/repository.spring.xml file and make the following changes.
From:
<bean id="singleTenantAuthenticatedAuthorityName" class="java.lang.String">
<constructor-arg value="Authenticated" />
</bean>To:
<bean id="singleTenantAuthenticatedAuthorityName" class="java.lang.String">
<constructor-arg value="pentahoUsers" />
</bean>From:
<bean id="singleTenantAdminAuthorityName" class="java.lang.String">
<constructor-arg value="Admin" />
</bean>To:
<bean id="singleTenantAdminAuthorityName" class="java.lang.String">
<constructor-arg value="pentahoAdmins" />
</bean>With LDAP authentication, the PDI Repository Explorer is empty
To fix the problem, you will have to delete the security settings established with the previously used authentication method, which will force the Pentaho Server to regenerate them for LDAP.
Procedure
Stop the Pentaho Server.
Delete the security and default directories from the following directory: /pentaho-solutions/system/jackrabbit/repository/workspaces/
Start the Pentaho Server.
Results
LDAP incorrectly authenticates user IDs that do not match letter case
Perform the following steps to force case-sensitivity for user names and fix this potential security risk:
Procedure
Stop the Pentaho Server.
Edit the /pentaho/server/pentaho-server/pentaho-solutions/system/applicationContext-spring-security-ldap.xml file.
Find
<bean class="org.pentaho.platform.plugin.services.security.userrole.ldap.DefaultLdapAuthenticationProvider">, and below the last</constructor-arg>element therein, and add the<property>definition shown in the following example:<property name="userDetailsContextMapper"> <ref bean="ldapContextMapper" /> </property>After the
</bean>tag fordaoAuthenticationProvider, add the following bean definition, changing theldapUsernameAttributefromsamAccountNameto the value that matches your environment:<bean id="ldapContextMapper" class="org.pentaho.platform.engine.security.UseridAttributeLdapContextMapper"> <property name="ldapUsernameAttribute" value="samAccountName" /> </bean>Start the Pentaho Server.
Results
Connection timeout issues when using CAS
Procedure
Stop the Pentaho Server.
Navigate to the pentaho-server/tomcat/webapps/pentaho/WEB-INF directory and open the web.xml file with any text editor.
Find the
session-configproperty and edit thesession-timeoutvalue (the default value is 120 minutes) to increase the period to a value that is greater than the setting used for your CAS server session timeout value:<session-config> <tracking-mode>COOKIE</tracking-mode> <session-timeout>120</session-timeout> </session-config>
Locate the Pentaho Web Context Filter and add the following
init-param:<init-param> <param-name>ssoEnabled</param-name> <param-value>true</param-value> </init-param
Save and close the file.
Activate the session timeout dialog box:
- Navigate to the
pentaho-server/pentaho-solutions/system
directory and open the
applicationContext-spring-security-cas.xml file
then locate the
httpSessionPentahoSessionContextIntegrationFilterbean id. - Find the
ssoEnabledproperty and set the value from true to false. - Save and close the file.
- Navigate to the
pentaho-server/pentaho-solutions/system
directory and open the
applicationContext-spring-security-cas.xml file
then locate the
Restart the Pentaho Server.
Results
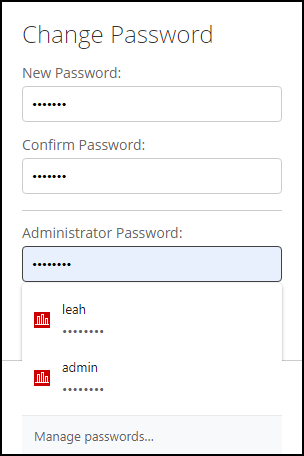
Cannot change Administrator password in PUC
Snowflake logging errors
Snowflake users see the warning message WARNING: Connect strings must start with jdbc:snowflake:// while connecting to Snowflake.
Pentaho 9.5 upgraded the Snowflake JDBC driver version to 3.13.29 to address security concerns.
To resolve this warning message, download the Snowflake JDBC driver version 3.13.30 from https://repo1.maven.org/maven2/net/snowflake/snowflake-jdbc/3.13.30/snowflake-jdbc-3.13.30.jar and replace the jar in the server: pentaho-server/tomcat/webapps/pentaho/WEB-INF/lib/ directory.
